* Build docker image upfront in CI and use it in integration tests. Previously, the development workflow was broken because the container generated from Dockerfile.CI was used in dev environments but the binary was not pre-built as it is on buildkite. I propose to just remove that image and use the "to be published" image instead in integration tests. This will have several advantages: - Fix the dev workflow. - Remove CI arch from authelia-scripts build command - Optimize CI time in buildkite since we'll cache a way small artifact - We don't build authelia more than once for earch arch. * Fix suites and only build ARM images on master or tagged commits * Optimise pipeline dependencies and Kubernetes suite to utilise cache * Run unit tests and docker image build in parallel. * Fix suite trying to write on read only fs. Co-authored-by: Amir Zarrinkafsh <nightah@me.com> |
||
|---|---|---|
| .buildkite | ||
| cmd | ||
| docs | ||
| example | ||
| internal | ||
| web | ||
| .dockerignore | ||
| .gitignore | ||
| bootstrap.sh | ||
| BREAKING.md | ||
| CHANGELOG.md | ||
| config.template.yml | ||
| docker-compose.yml | ||
| Dockerfile | ||
| Dockerfile.arm32v7 | ||
| Dockerfile.arm64v8 | ||
| go.mod | ||
| go.sum | ||
| LICENSE | ||
| README.md | ||
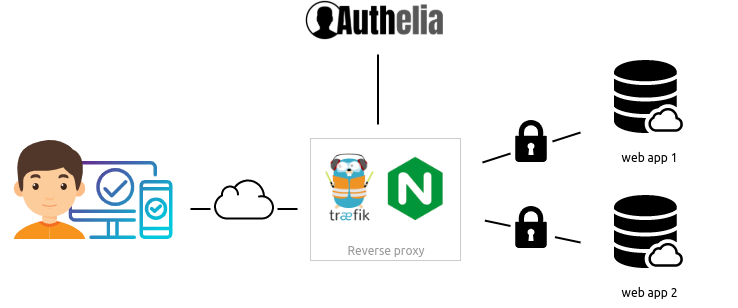
Authelia is an open-source authentication and authorization server providing 2-factor authentication and single sign-on (SSO) for your applications via a web portal. It acts as a companion of reverse proxies like nginx or Traefik to tell them wether queries should pass through. Unauthenticated user are redirected to Authelia Sign-in portal instead.
The architecture is shown in the diagram below.
BREAKING NEWS: Authelia v4 has been released! Please read BREAKING.md if you want to migrate from v3 to v4. Otherwise, start fresh in v4 and enjoy!
Authelia can be installed as a standalone service using Docker or NPM but can also be deployed easily on Kubernetes leveraging ingress controllers and ingress configuration.

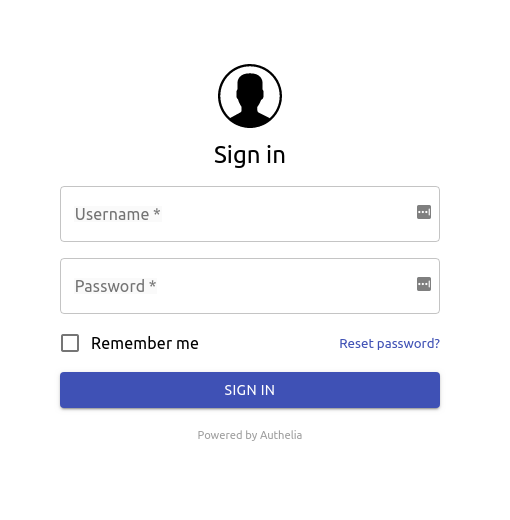
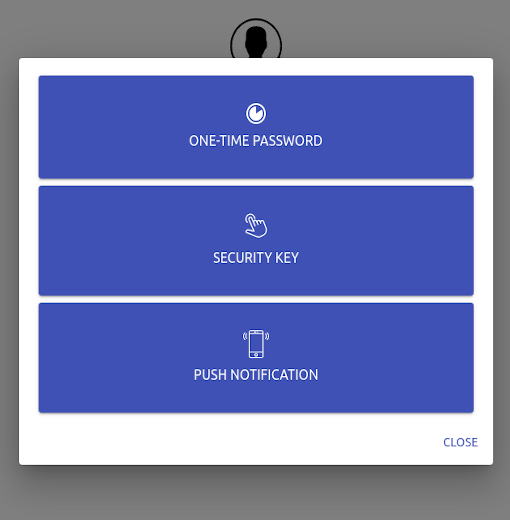
Here is what Authelia's portal looks like
Features summary
Here is the list of the main available features:
- Several kind of second factor:
- Password reset with identity verification using email confirmation.
- Single-factor only authentication method available.
- Access restriction after too many authentication attempts.
- Fine-grained access control per subdomain, user, resource and network.
- Support of basic authentication for endpoints protected by single factor.
- Highly available using a remote database and Redis as a highly available KV store.
- Compatible with Kubernetes ingress-nginx controller out of the box.
For more details about the features, follow Features.
Proxy support
Authelia works in combination with nginx, Traefik or HAProxy. It can be deployed on bare metal with Docker or directly in Kubernetes.




Getting Started
You can start off with
git clone https://github.com/authelia/authelia.git && cd authelia
source bootstrap.sh
If you want to go further, please read Getting Started.
Deployment
Now that you have tested Authelia and you want to try it out in your own infrastructure, you can learn how to deploy and use it with Deployment. This guide will show you how to deploy it on bare metal as well as on Kubernetes.
Security
If you want more information about the security measures applied by Authelia and some tips on how to set up Authelia in a secure way, refer to Security.
Changelog & Breaking changes
See CHANGELOG.md and BREAKING.md.
Contribute
Anybody willing to contribute to the project either with code, documentation, security reviews or whatever, are very welcome to issue or review pull requests and take part to discussions in Gitter.
I am very grateful to contributors for their contributions to the project. Don't hesitate, be the next!
Build Authelia
If you want to contribute with code, you should follow the documentation explaining how to build the application.
License
Authelia is licensed under the Apache 2.0 license. The terms of the license are detailed in LICENSE.





