In order to redirect the user after authentication, Authelia uses rd query parameter provided by the proxy. However an attacker could use phishing to make the user be redirected to a bad domain. In order to avoid the user to be redirected to a bad location, Authelia now verifies the redirection URL is under the protected domain. |
||
|---|---|---|
| client | ||
| docs | ||
| example | ||
| images | ||
| scripts | ||
| server | ||
| shared | ||
| test | ||
| .gitignore | ||
| .npmignore | ||
| .travis.yml | ||
| CHANGELOG.md | ||
| config.minimal.yml | ||
| config.template.yml | ||
| CONTRIBUTORS.md | ||
| docker-compose.dev.yml | ||
| docker-compose.dockerhub.yml | ||
| docker-compose.minimal.yml | ||
| docker-compose.swarm.minimal.yml | ||
| docker-compose.test.yml | ||
| docker-compose.yml | ||
| Dockerfile | ||
| Dockerfile.dev | ||
| Gruntfile.js | ||
| LICENSE | ||
| package-lock.json | ||
| package.json | ||
| README.md | ||
| users_database.yml | ||

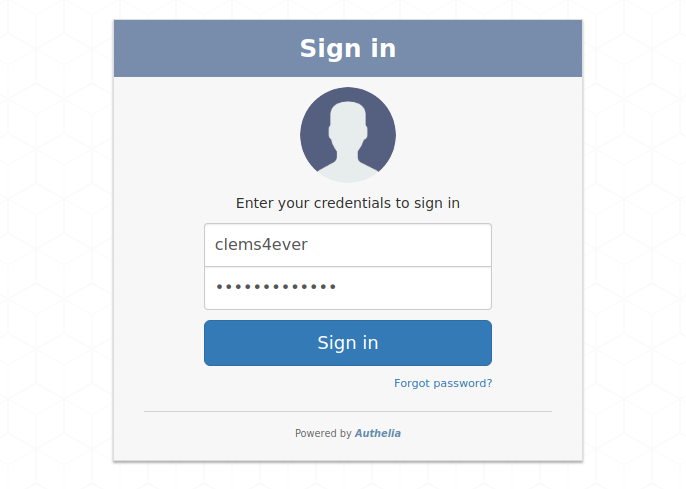
Authelia is an open-source authentication and authorization providing 2-factor authentication and single sign-on (SSO) for your applications. It acts as a companion of reverse proxies by handling authentication and authorization requests.
Authelia can be installed as a standalone service using Docker or NPM but can also be deployed easily on Kubernetes. On the latest, one can leverage ingress configuration to set up authentication and authorizations for specific services in only few seconds.

Features summary
Here is the list of the main available features:
- U2F - Universal 2-Factor - support with Yubikey.
- TOTP - Time-Base One Time password - support with Google Authenticator.
- Password reset with identity verification using email.
- Single-factor only authentication method available.
- Access restriction after too many authentication attempts.
- User-defined access control per subdomain and resource.
- Support of [basic authentication] for endpoints protected by single factor.
- High-availability using distributed database and KV store.
- Compatible with Kubernetes ingress-nginx controller out of the box.
For more details about the features, follow Features.
Getting Started
If you want to quickly test Authelia with Docker, we recommend you read Getting Started.
Deployment
Now that you have tested Authelia and you want to try it out in your own infrastructure, you can learn how to deploy and use it with Deployment. This guide will show you how to deploy it on bare metal as well as on Kubernetes.
Security
If you want more information about the security measures applied by Authelia and some tips on how to set up Authelia in a secure way, refer to Security.
Changelog
See CHANGELOG.md.
Contribute
Anybody willing to contribute to the project either with code, documentation, security reviews or whatever, are very welcome to issue or review pull requests and take part to discussions in Gitter.
We are already greatful to contributors listed in CONTRIBUTORS.md for their contributions to the project. Be the next in the list!
Build Authelia
If you want to contribute with code, you should follow the documentation explaining how to build the application.
Donation
Wanna see more features? Then fuel us with a few beers!
License
Authelia is licensed under the MIT License. The terms of the license are as follows:
The MIT License (MIT)
Copyright (c) 2016 - Clement Michaud
Permission is hereby granted, free of charge, to any person obtaining a copy
of this software and associated documentation files (the "Software"), to deal
in the Software without restriction, including without limitation the rights
to use, copy, modify, merge, publish, distribute, sublicense, and/or sell
copies of the Software, and to permit persons to whom the Software is
furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in
all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY,
FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE
AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY,
WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN
CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.



